Empowering Women’s Health with Dr. Holly Lucille
Women’s health is a critical aspect of overall well-being and is essential for the proper functioning of society as a whole. The health of…
The Rise of Tylar Witt: A Rising Star in the Entertainment Industry
Tylar Witt’s journey to stardom began in a small town in the Midwest, where she discovered her passion for performing at a young age.…
The Classic Winchester Model 1897: A Timeless Shotgun
The Winchester Model 1897, also known as the M97 or simply the 97, is a pump-action shotgun that was designed by John Browning. It…
The Rise of Protogen Fursuits: A New Frontier in Furry Fashion
The origins of Protogen fursuits can be traced back to the furry community, a subculture interested in anthropomorphic animal characters. The concept of Protogen…
Rock the Look: Pink Leather Pants
Pink leather pants are a bold and stylish fashion statement that can add a pop of color and edginess to any outfit. Whether you’re…
Miniature Bernedoodle: The Perfect Small-Sized Companion
The Miniature Bernedoodle is a crossbreed between a Bernese Mountain Dog and a Miniature Poodle. This adorable and affectionate dog is gaining popularity among…
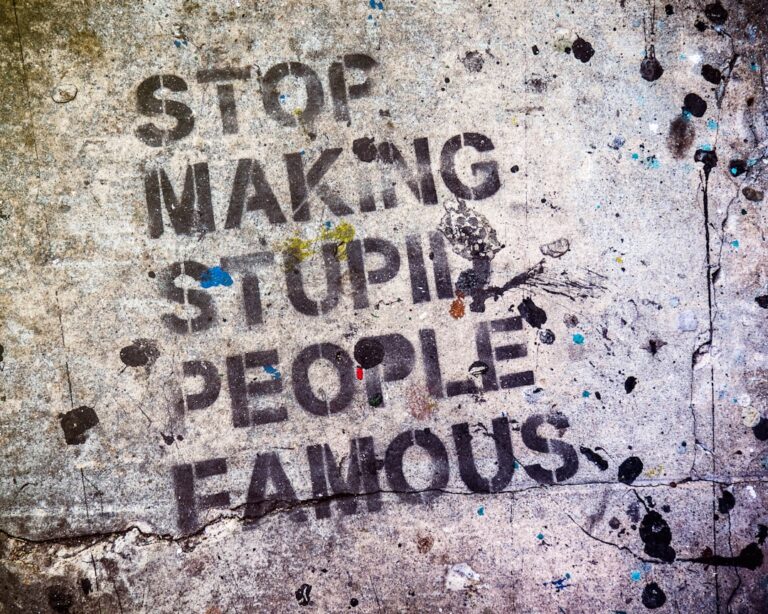
Back Alley Tales: A Glimpse into the Underbelly of the City
Back alleys have long been a mysterious and intriguing part of urban landscapes. These narrow, often dimly lit passageways have a reputation for being…
Maximizing Air Quality with Charcoal Canister
Air quality refers to the condition of the air within our environment, including the presence of pollutants and other harmful substances. Poor air quality…
Uncovering the Science of Smithfield’s Sustainable Practices
Smithfield Foods is a leading global food company that is committed to producing high-quality, sustainable food products. With a focus on environmental stewardship, animal…
Dunedin High School: Fostering Academic Excellence
Dunedin High School is a prestigious educational institution located in the heart of Dunedin, Florida. Established in 1926, the school has a rich history…